Este curso de treinamento oferece um estudo amplo dos controles e técnicas de segurança no Google Cloud. Através de apresentações, demonstrações e laboratórios, você explora e implementa os componentes de uma solução segura do Google Cloud. Você utiliza serviços incluindo Cloud Identity, Identity and Access Management (IAM), Cloud Load Balancing, Cloud IDS, Web Security Scanner, BeyondCorp Enterprise e Cloud DNS.
Objetivos
Neste curso, os participantes aprenderão as seguintes habilidades:
- Identificar os fundamentos da segurança do Google Cloud. Gerenciar identidades de administração com o Google Cloud.
- Implementar administração de usuários com Identity and Access Management (IAM).
- Configurar Redes Virtuais Privadas (VPCs) para isolamento, segurança e registro.
- Aplicar técnicas e melhores práticas para gerenciar com segurança o Compute Engine.
- Aplicar técnicas e melhores práticas para gerenciar com segurança os dados do Google Cloud.
- Aplicar técnicas e melhores práticas para proteger aplicativos do Google Cloud.
- Aplicar técnicas e melhores práticas para proteger recursos do Google Kubernetes Engine (GKE).
- Gerenciar proteção contra ataques de negação de serviço distribuídos (DDoS).
- Gerenciar vulnerabilidades relacionadas ao conteúdo.
- Implementar soluções de monitoramento, registro, auditoria e escaneamento do Google Cloud.
Público-Alvo
Esta classe é direcionada ao seguinte público:
- Analistas, arquitetos e engenheiros de segurança da informação em nuvem.
- Especialistas em segurança da informação ou cibersegurança.
- Arquitetos de infraestrutura em nuvem.
Pré-requisitos
Para aproveitar ao máximo este curso, os participantes precisam atender aos seguintes critérios:
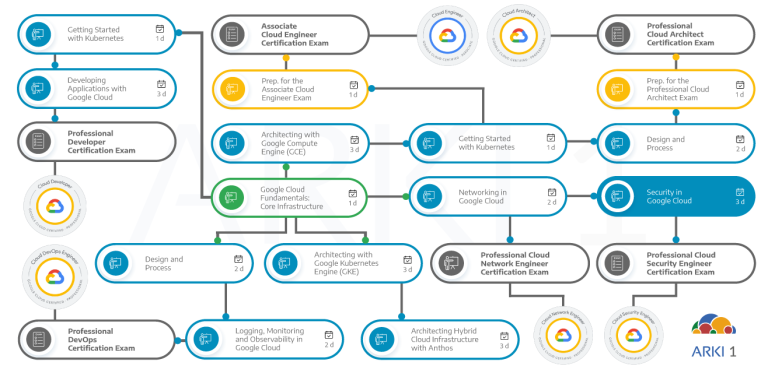
- Conclusão do Google Cloud Fundamentals: Core Infrastructure ou experiência equivalente.
- Conclusão prévia do curso Networking no Google Cloud ou possuir experiência equivalente.
- Conhecimento de conceitos fundamentais em segurança da informação, por meio de experiência ou treinamento online como SANS SEC301: Introdução à Segurança Cibernética.
- Proficiência básica com ferramentas de linha de comando e ambientes de sistema operacional Linux.
- Experiência em operações de sistemas, incluindo implantação e gerenciamento de aplicativos, seja localmente ou em um ambiente de nuvem pública.
- Compreensão de leitura de código em Python ou JavaScript.
- Compreensão básica do terminologia do Kubernetes (preferível, mas não obrigatório).
Duração
24 horas (3 dias)
Investimento
Consulte o valor atualizado e próximas datas para turmas abertas em nossa página de inscrições. Caso tenha interesse em uma turma fechada para sua empresa, entre em contato conosco.
Resumo do curso
O curso inclui apresentações, demonstrações e laboratórios práticos.
- Explain the shared security responsibility model of Google Cloud.
- Describe how Google Cloud approaches security.
- Recognize threats mitigated by Google and Google Cloud.
- Identify Google Cloud’s commitments to regulatory compliance.
- Describe what Cloud Identity is and what it does.
- Explain how Google Cloud Directory Sync securely syncs users and permissions between your on-premises LDAP or AD server and the cloud.
- Explore and apply best practices for managing groups, permissions, domains, and administrators with Cloud Identity.
- Identify IAM roles and permissions that can be used to organize resources in Google Cloud.
- Explain the management-related features of Google Cloud projects.
- Define IAM policies, including organization policies.
- Implement access control with IAM.
- Provide access to Google Cloud resources by using predefined and custom IAM roles.
- Describe the function of VPC networks.
- Recognize and implement best practices for configuring VPC firewalls (both ingress and egress rules).
- Secure projects with VPC Service Controls.
- Apply SSL policies to load balancers.
- Enable VPC flow logging, and then use Cloud Logging to access logs.
- Deploy Cloud IDS, and view threat details in the Google Cloud console.
- Create and manage service accounts for Compute Engine instances (default and customer-defined).
- Detail IAM roles and scopes for VMs.
- Explore and apply best practices for Compute Engine instances.
- Explain the function of the Organization Policy Service.
- Use IAM permissions and roles to secure cloud resources.
- Create and wrap encryption keys using the Compute Engine RSA public key certificate.
- Encrypt and attach persistent disks to Compute Engine instances.
- Manage keys and encrypted data by using Cloud Key Management Service (Cloud KMS) and Cloud HSM.
- Create BigQuery authorized views.
- Recognize and implement best practices for configuring storage options.
- Recall various types of application security vulnerabilities.
- Detect vulnerabilities in App Engine applications by using Web Security Scanner.
- Secure Compute Engine Applications by using BeyondCorp Enterprise.
- Secure application credentials by using Secret Manager.
- Identify the threats of OAuth and Identity Phishing.
- Explain the differences between Kubernetes service accounts and Google service accounts.
- Recognize and implement best practices for securely configuring GKE.
- Explain logging and monitoring options in Google Kubernetes Engine.
- Identify the four layers of DDoS Mitigation.
- Identify methods Google Cloud uses to mitigate the risk of DDoS for its customers.
- Use Google Cloud Armor to blocklist an IP address and restrict access to an HTTP Load Balancer.
- Discuss the threat of ransomware.
- Explain ransomware mitigations strategies (backups, IAM, Cloud Data Loss Prevention API).
- Highlight common threats to content (data misuse; privacy violations; sensitive, restricted, or unacceptable content).
- Identify solutions for threats to content (classification, scanning, and redacting).
- Detect and redact sensitive data by using the Cloud DLP API.
- Explain and use the Security Command Center.
- Apply Cloud Monitoring and Cloud Logging to a project.
- Apply Cloud Audit Logs to a project.
- Identify methods for automating security in Google Cloud environments.